Request assembly / context selection — attack surface (summary)
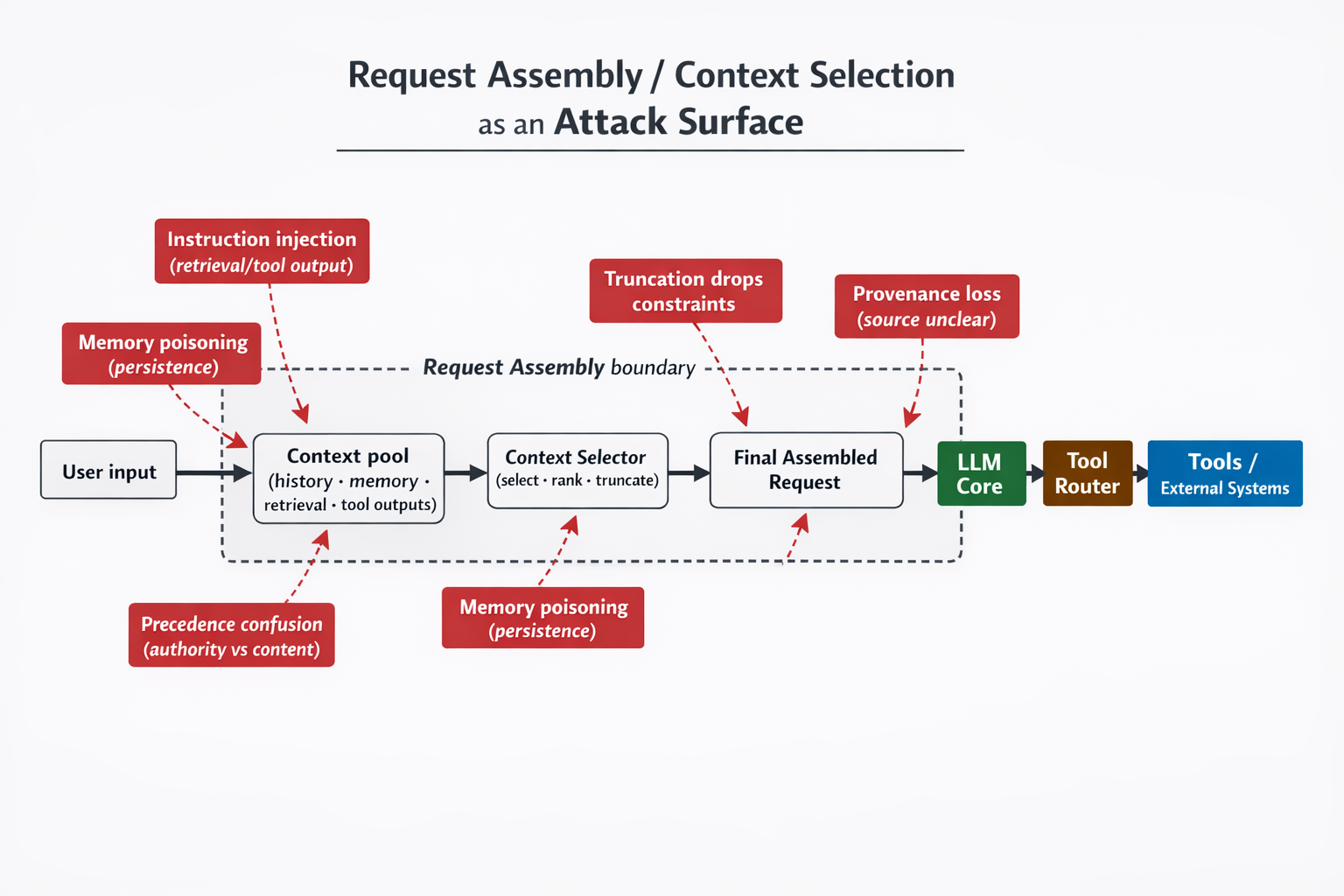
Overview
A generic reference model for the request-assembly boundary (context aggregation → selection/ranking → truncation) that precedes an LLM call.
Text alternative (long description)
- Left-to-right flow: User input → Context pool → Context selector → Final assembled request → LLM core → Tool router → Tools / external systems.
- A dashed rectangle labeled Request assembly boundary encloses: Context pool, Context selector, Final assembled request.
- Risk callouts:
- Instruction injection (retrieval/tool output) pointing into the context pool.
- Memory poisoning (persistence) pointing into the context pool and the context selector.
- Precedence confusion (authority vs content) pointing into the context pool.
- Truncation drops constraints pointing into the final assembled request.
- Provenance loss (source unclear) pointing near the handoff to the LLM core.
Scope and limitations
- Vendor-agnostic reference model; not a claim about any specific product implementation.
- Risk labels are review targets (checklist), not assertions.